CrowdStrike MDR Implementation: What Actually Changes Once It Goes Live
Security teams rarely struggle with buying technology. They struggle with what happens after it lands.
CrowdStrike MDR Implementation is often discussed as if it were a straightforward deployment. Install the agent. Integrate identity. Tune policies. Hand over monitoring. Job done.
In reality, it doesn’t work that way.
Once CrowdStrike moves from contract to console, operational realities surface quickly. Processes that looked stable begin to show gaps. Detection logic collides with legacy infrastructure. Internal ownership becomes blurred. Expectations harden. The difference between a clean implementation and a disruptive one rarely comes down to tooling. It comes down to how the organisation absorbs it.
The Shift from Tool to Operating Model
CrowdStrike is not just an endpoint platform. It becomes part of the detection and response fabric. When MDR is layered on top, it alters accountability in subtle ways.
Security teams often assume they are outsourcing alert handling. In reality, they are entering a shared response model. The MDR provider investigates. The internal team still owns remediation decisions, change control, communications and business risk acceptance.
This is where friction appears.
If escalation paths are vague, incidents stall. If asset inventory is incomplete, telemetry loses context. If identity hygiene is weak, detection rules generate noise. None of these are product failures. They are operational mismatches exposed by implementation.
CrowdStrike MDR Implementation therefore has less to do with installation and more to do with alignment.
What Tends to Surface During Deployment
Every environment carries technical debt. MDR makes that debt visible.
Unmanaged endpoints appear. Legacy operating systems refuse modern agent versions. Service accounts with excessive privilege trigger behaviour alerts. Poorly segmented networks inflate investigation scope.
There is also the question of logging maturity. Organisations that have relied heavily on perimeter defences sometimes discover limited visibility into east west traffic. MDR analysts compensate, but response precision improves significantly when endpoint data is complemented by identity and network signals.
Another recurring issue sits outside technology. It involves response discipline. Some organisations have well-rehearsed playbooks but rarely test them. Others rely on informal escalation chains. Once MDR begins feeding actionable alerts, those weaknesses cannot hide.
The implementation phase often becomes the first true stress test of incident response governance.
Where Implementation Succeeds or Fails
CrowdStrike MDR Implementation tends to succeed when three conditions exist.
- There is clarity on what the service will and will not do. Expectations are documented, not assumed.
- There is a defined internal owner for security operations, even if that function is small. Someone must interpret business impact.
- And there is executive tolerance for visibility. MDR brings uncomfortable transparency. Leadership must accept that detection maturity may temporarily make risk feel larger, not smaller.
When these conditions are missing, friction builds quietly. Alerts are questioned rather than actioned. Escalations feel intrusive. Confidence erodes.
A Practical Flow of How the Model Operates
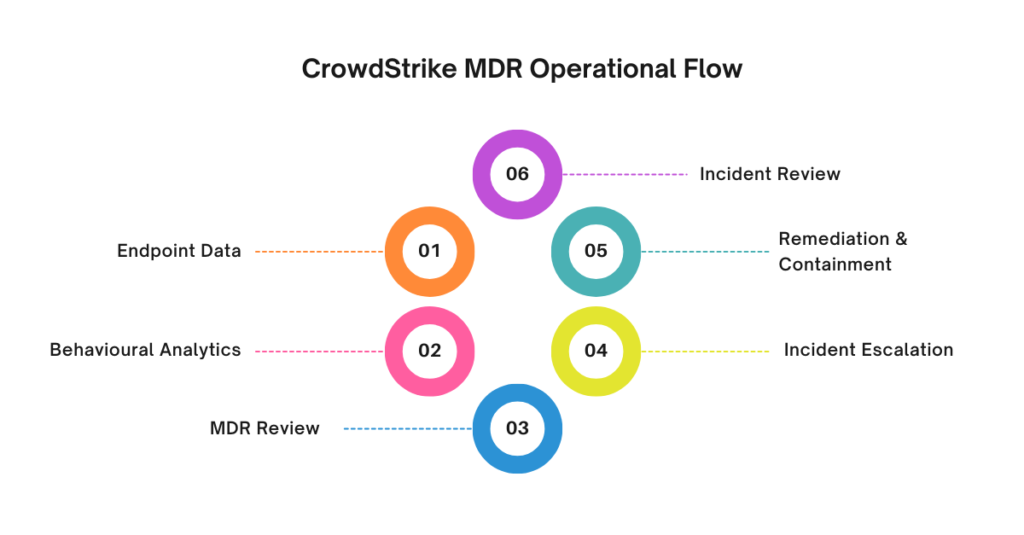
The operational flow can be visualised clearly. This is often useful when briefing leadership or mapping responsibilities.
- Endpoint telemetry is collected through the Falcon agent across servers and workstations.
- Behavioural analytics and threat intelligence correlate activity in the platform.
- MDR analysts review suspicious patterns and validate threats.
- Confirmed incidents are escalated with context, recommended containment steps and severity grading.
- Internal teams execute remediation, isolation, credential resets or broader containment measures.
- Post incident review feeds tuning decisions and control improvements.
This sequence looks straightforward. In practice, step five determines whether the entire chain works. Technical containment is rarely blocked by tooling. It is blocked by change windows, business approval layers, or fear of operational disruption.
Integration Realities
CrowdStrike rarely operates in isolation. It connects with identity providers, SIEM platforms, vulnerability scanners, ticketing systems and sometimes legacy SOC tooling.
Integration introduces complexity.
API permissions must be carefully scoped. Alert duplication between systems needs rationalisation. Workflow routing requires thought. Without coordination, analysts end up triaging the same event in multiple platforms.
Identity integration deserves particular care. Modern attacks lean heavily on credential abuse. Linking endpoint telemetry with identity context enhances detection quality. Poor directory hygiene, however, dilutes that value.
Implementation teams often underestimate the time required to stabilise integrations. The product may be live in days. Operational harmony can take weeks.
The Human Element That Rarely Gets Discussed
There is a subtle cultural impact when MDR goes live.
Internal analysts may feel displaced. IT teams may perceive increased scrutiny. Executives may expect instant risk reduction.
None of this is malicious. It is normal reaction to change.
Clear communication reduces tension. It helps to position MDR as an extension of capability rather than oversight. It also helps to clarify that detection volume does not equate to failure. Mature visibility often reveals more activity than anticipated.
Some organisations experience an initial spike in high severity alerts. Not because risk increased overnight, but because blind spots narrowed.
That adjustment period requires steady handling.
Lessons Drawn from Wider Industry Shifts
Over the past few years, high profile intrusions have reinforced a simple truth. Prevention alone is fragile.
Incidents such as the exploitation of identity and cloud misconfiguration during the SolarWinds supply chain attack exposed the limits of perimeter-based thinking. Endpoint and behavioural visibility became central to detection strategy.
Vendors like CrowdStrike built momentum on that shift. Managed detection services grew as organisations recognised the shortage of skilled analysts and the speed of modern threats.
CrowdStrike MDR Implementation therefore sits within a broader transformation. It is not simply tool adoption. It reflects acceptance that continuous monitoring must operate with external expertise.
Yet outsourcing detection does not remove internal responsibility. Governance, risk appetite, and remediation authority remain in house.
Measuring Whether Implementation Worked
Success is rarely measured by the absence of alerts.
More realistic indicators include reduced dwell time. Faster containment decisions. Clearer escalation ownership. Fewer ambiguous handoffs between IT and security.
There is also the question of board level confidence. When reporting becomes consistent and backed by validated incident analysis, security discussions become more grounded.
Organisations sometimes expect cost reduction as a primary outcome. That expectation can mislead. The real return lies in improved detection accuracy and structured response, not immediate headcount savings.
Common Pitfalls That Quietly Undermine Value
One recurring mistake is underscoping assets during deployment. Shadow IT often remains uncovered. That gap becomes visible only after an incident touches an unmanaged endpoint.
Another issue arises when policy tuning is neglected after going live. Behavioural models require calibration. Ignoring tuning leads to fatigue.
There is also over reliance on automation. While containment actions can be automated, blanket automation without context risks business disruption.
CrowdStrike MDR Implementation should not be rushed to meet reporting milestones. Rushed deployment leaves fragile integration points that surface later under pressure.
The Balance Between Visibility and Stability
MDR brings sharper visibility. That clarity can feel uncomfortable. It challenges long held assumptions about security posture.
Organisations that treat implementation as a technical rollout miss this strategic layer. Those that treat it as an operational evolution extract more value.
The distinction may seem subtle but it’s not.
Conclusion
CrowdStrike MDR Implementation is less about installing an agent and more about reshaping detection and response discipline. The technology is mature. The complexity lies in governance, integration, and operational readiness.
Organisations considering the move should examine escalation ownership, asset visibility, identity hygiene and executive expectations before going live. These factors influence outcome more than feature comparison.
CyberNX is a trusted CrowdStrike services partner and can help you make the decision as well as CrowdStrike consulting. They can help you deploy and manage Falcon in your environment – with 24×7 support and MDR to respond to threats anytime. Their CrowdStrike consulting will also help you with endpoint security, identity protection, cloud security and data protection.
Handled properly, MDR strengthens response maturity. Handled casually, it becomes another console feeding alerts into an already stretched team. The difference is rarely technical. It is operational judgement.



Post Comment