Network Security Projects: How to Plan and Execute Successfully
In an era of sophisticated cyber threats and decentralized workforces, network security can no longer be an afterthought.
Building a resilient defense requires more than just deploying tools; it demands a structured, lifecycle-based approach to planning and execution.
A well-executed project ensures that security becomes an enabler of business continuity rather than a bottleneck for performance.
The Network Security Project Lifecycle
A successful security deployment follows a rigorous progression from discovery to implementation.
Skipping phases in this lifecycle often leads to configuration gaps that attackers can easily exploit.
Risk Assessment: Identifying blind spots in current topology.
The foundation of any security project is a comprehensive risk assessment. This phase involves a deep dive into the existing network map to identify “shadow IT,” unprotected entry points, and legacy hardware that no longer receives security patches.
By auditing traffic flows and asset inventories, engineers can pinpoint exactly where the current topology is most vulnerable, whether it is an unmonitored IoT device or an over-privileged guest network.
Architecture Development: Designing segmented networks ready for scalability.
Once risks are identified, the focus shifts to designing a future-proof architecture. Modern security design relies on network segmentation, which divides the network into smaller, isolated zones to prevent lateral movement by attackers.
This stage ensures the blueprint is not only secure but also scalable, allowing the organization to add new branches, cloud instances, or users without compromising the integrity of the core security posture.
Critical Components in Modern Projects
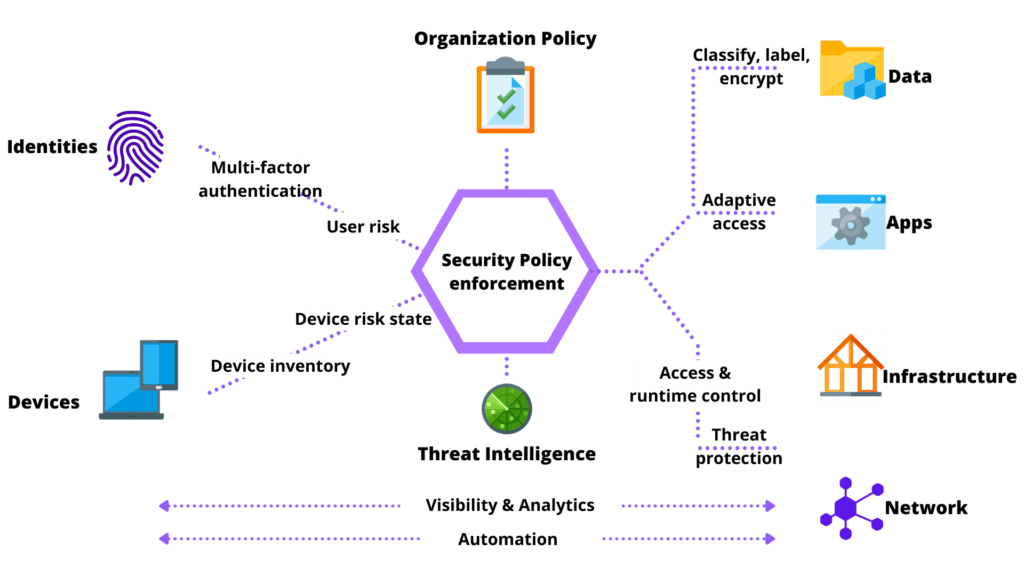
Modern network security projects must address the disappearance of the traditional office perimeter.
The integration of advanced hardware and identity-centric policies is vital for protecting data in a distributed environment.
Edge Security: Implementing SD-WAN and Next-Generation Firewalls (NGFW).
The network edge is the first line of defense. Implementing Next-Generation Firewalls (NGFW) provides deep packet inspection and integrated intrusion prevention (IPS) that traditional firewalls lack.
When combined with SD-WAN (Software-Defined Wide Area Network), organizations can securely route traffic across multiple connection types (MPLS, LTE, Broadband) while maintaining consistent security policies and optimizing application performance across all locations.
Identity and Access Protection: Projects focused on Zero Trust and MFA.
In a modern project, the user’s identity is the new perimeter. Shifting toward a Zero Trust architecture means that no entity, inside or outside the network, is trusted by default.
Execution involves implementing Multi-Factor Authentication (MFA) across all access points and ensuring that every request is strictly verified based on user identity, device health, and context before granting access to specific network resources.
Data Encryption in Transit: Applying RSA protocols and secure VPN tunneling.
Protecting data as it moves across public and private networks is non-negotiable. This component focuses on deploying robust encryption standards, such as RSA algorithms for secure key exchange and advanced VPN tunneling (IPsec or SSL/TLS).
These protocols ensure that even if data is intercepted during transit, it remains encrypted and useless to unauthorized parties, maintaining the confidentiality of sensitive corporate communications.
Challenges of Multi-location Projects (Global Roll-out)
Deploying security infrastructure across international borders introduces layers of complexity that go beyond technical configuration, involving compliance, culture, and logistics.
How to standardize security across offices in Brazil, USA, Europe, and Asia.
Achieving a uniform security posture globally is a significant challenge. Differences in local regulations and varying internet service quality require a centralized policy management approach.
Standardizing hardware stacks and software-defined policies ensures that an office in São Paulo maintains the exact same security rigor as a branch in London or Singapore, simplifying global monitoring and incident response.
Vendor management and international hardware logistics.
Executing a global roll-out requires meticulous supply chain management. Different countries have varying import taxes, certification requirements, and lead times.
Successful execution depends on managing multiple vendors and local distributors to ensure that firewalls, switches, and APs arrive on-site, pre-configured, and compliant with local laws to avoid project delays and budget overruns.
The Importance of the Homologation and Testing Phase
The final stage of a project determines its long-term viability. Without rigorous validation, a newly implemented security system might break critical business workflows or contain hidden misconfigurations.
How to perform infrastructure migration without productivity impact (Zero Downtime).
Transitioning to a new security infrastructure must be invisible to the end-user. Achieving Zero Downtime involves parallel running (keeping the old and new systems active simultaneously), meticulous cutover scheduling during off-peak hours, and automated rollback plans. This ensures that the migration improves security without causing costly interruptions to daily business operations.
Penetration testing and security policy validation after implementation.
The project is not complete until the new defenses are tested under “fire.” Penetration testing (Pen Testing) is used to simulate real-world attacks against the newly implemented architecture to find any remaining cracks.
Simultaneously, every security policy, from firewall rules to MFA prompts, must be validated to ensure they function exactly as designed, providing the final assurance that the project has met its security objectives.



Post Comment